Attention, cet article a plus d'une année d'ancienneté. Il est possible que les informations présentées ne soient plus à jour, spécialement dans le cadre d'un article technique.
Hi everyone,
After a twitter chat with @PunKeel, I’ve learned that Let’s Encrypt now provide ECDSA certificate. I’m interested by that because ECDSA are much less resources consuming than “old” RSA certificate.
This is better for your server and your visitors.
However, it’s kind of complicated. Official client are nor documented, nor fully and easily compatible with ECDSA certificate generation. Braces yourselves.
First of all, download the Let’s Encrypt client and launch it:
cd /etc git clone https://github.com/letsencrypt/letsencrypt cd letsencrypt ./letsencrypt-auto --help
Now; for the rest of the how-to, please change abyssproject.net and www.abyssproject.net by your domain name.
Create necessary folders:
mkdir /etc/letsencrypt/live-ecdsa/ mkdir /etc/letsencrypt/live-ecdsa/abyssproject.net cd /etc/letsencrypt/live-ecdsa/abyssproject.net mkdir letmp
Wait, I’m using secp384r1 curve in this example, she should adapt to every need. You can check all available curves on OpenSSL with this command:
openssl ecparam -list_curves
Now, create the private key for your certificate and indicate the curve wanted:
openssl ecparam -genkey -name secp384r1 > privkey-p384.pem
Now create your CSR (please indicate your own domain):
openssl req -new -sha256 -key privkey-p384.pem -subj "/CN=abyssproject.net" -reqexts SAN -config <(cat /etc/ssl/openssl.cnf <(printf "[SAN]\nsubjectAltName=DNS:abyssproject.net,DNS:www.abyssproject.net")) -outform der -out csr-p384.der
Go into the temp folder “letmp” and create your Let’s Encrypt certificate:
cd letmp /etc/letsencrypt/letsencrypt-auto certonly -a webroot --email mail@abyssproject.net --webroot-path /www/abyssproject.net/ --csr /etc/letsencrypt/live-ecdsa/abyssproject.net/csr-p384.der --renew-by-default --agree-tos cat 0001* > /etc/letsencrypt/live-ecdsa/abyssproject.net/chain.pem
If it works, simply enter the configuration in Nginx 🙂
ssl_certificate /etc/letsencrypt/live-ecdsa/abyssproject.net/chain.pem; ssl_certificate_key /etc/letsencrypt/live-ecdsa/abyssproject.net/privkey-p384.pem;
Just reload the webserver after that:
service nginx reload
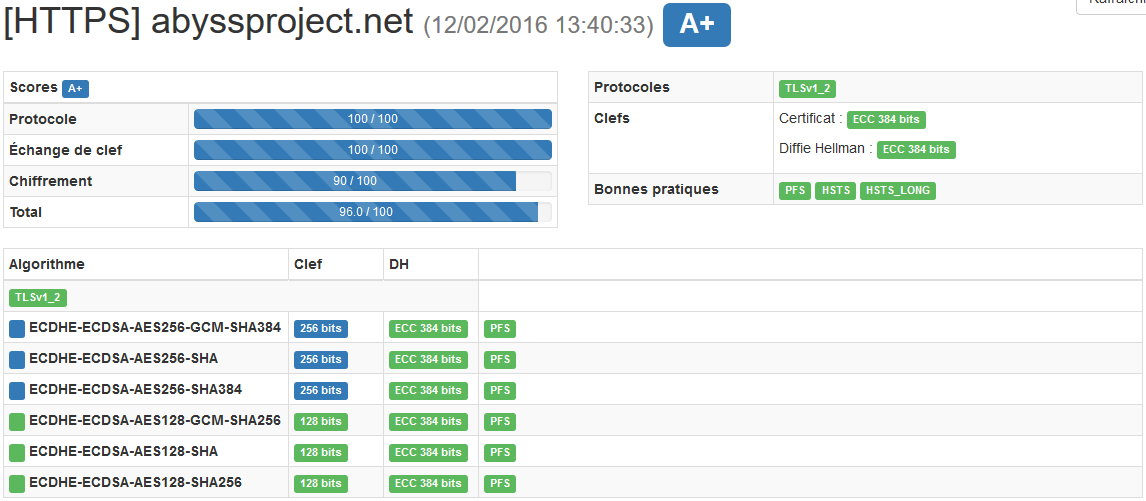
And now, you are using a ECDSA certificate (Test tool) 🙂

 (4 votes, moyenne: 4,00 sur 5)
(4 votes, moyenne: 4,00 sur 5)
Hello, thanks for this useful tutorial, what is necessary to regenerate certificate (extends to 3 months)
Hello, you need to do exactly the same thing but without regenerating the private key.